Why Wildcard Certificates Hide Production Failures
Wildcard certificates are convenient but create massive blast zones. Learn how an expiring wildcard takes down dozens of subdomains simultaneously.
A single wildcard certificate (*.yourdomain.com) is deeply convenient. With one cryptographic asset, you can secure your API, your staging environment, your customer dashboards, and your internal admin panels. But in system reliability, convenience is often the enemy of resilience.
Most incidents are not caused by a single failure. They are caused by tightly coupled components failing simultaneously. Wildcard certificates represent a massive, fragile single point of failure.
The Blast Radius of Expiration
When a tightly scoped SAN (Subject Alternative Name) certificate expires—for example, api.staging.yourdomain.com—only the staging API goes offline. The incident is localized.
When a wildcard certificate expires, the blast radius is catastrophic. Every single endpoint relying on that keypair fails at the exact same millisecond. Your public marketing site drops. Your payment API terminates handshakes. Even your internal deployment dashboards become unreachable, locking operations teams out of the very tools they need to fix the problem.
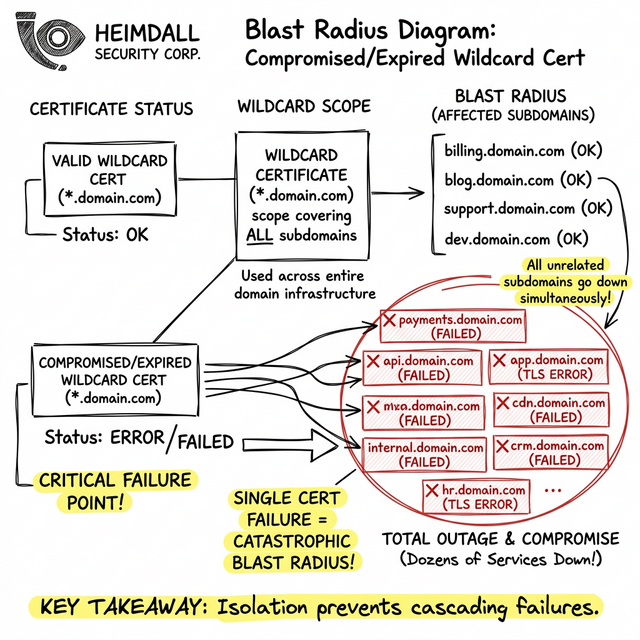
Security Compromise Cascades
Beyond expiration, wildcards introduce severe security implications. To use a wildcard across a distributed microservice architecture, the private key must be copied and distributed to multiple ingress controllers, load balancers, and external CDNs.
If a single edge node is compromised and the private key is extracted, the attacker can impersonate any subdomain. They aren't just intercepting staging traffic; they possess the cryptographic material to masquerade as your production authentication endpoints.
The Monitoring Challenge
Tracking wildcards is notoriously difficult because you cannot simply scan a zone file to know where the certificate is deployed. In practice, this usually fails because operations teams lose track of which legacy load balancers are still utilizing the old wildcard after a migration.
Mitigating the Risk with Granularity
The architectural best practice is to utilize granular, automatically renewed SAN certificates per service boundary.
To manage the increased volume of localized certificates, you cannot rely on manual tracking. Heimdall Observer provides comprehensive visibility into these granular endpoints. By explicitly monitoring every single subdomain individually, Heimdall ensures that each specific TLS scope is validated, giving your team control and safety without the catastrophic blast radius of a wildcard.
Senior Systems Reliability Engineer focused on uptime, incident response, and building monitoring systems that surface problems before users notice.
"Wir haben Heimdall Observer entwickelt, um genau die in diesem Artikel beschriebenen Probleme zu überwachen."