The Hidden Risks of Certificate Revocation (CRL & OCSP)
When a private key is compromised, revocation is suppose to protect you. Explore why CRLs and OCSP fail in production environments.

When a TLS private key is leaked or compromised, the certificate must be invalidated before its expiration date. The cryptographic ecosystem relies on Certificate Revocation Lists (CRL) and the Online Certificate Status Protocol (OCSP) to communicate this invalidation to clients.
However, in distributed networking, maintaining real-time global state is incredibly difficult. Because of this, revocation mechanisms frequently experience invisible failures.
How Revocation Attempts to Work
A CRL is simply a large, occasionally updated list of serial numbers that a CA has revoked. As the internet grew, downloading massive lists became unsustainable. OCSP was invented to solve this, allowing clients to query a CA responder in real-time to check the status of a specific certificate.
The Soft-Fail Compromise
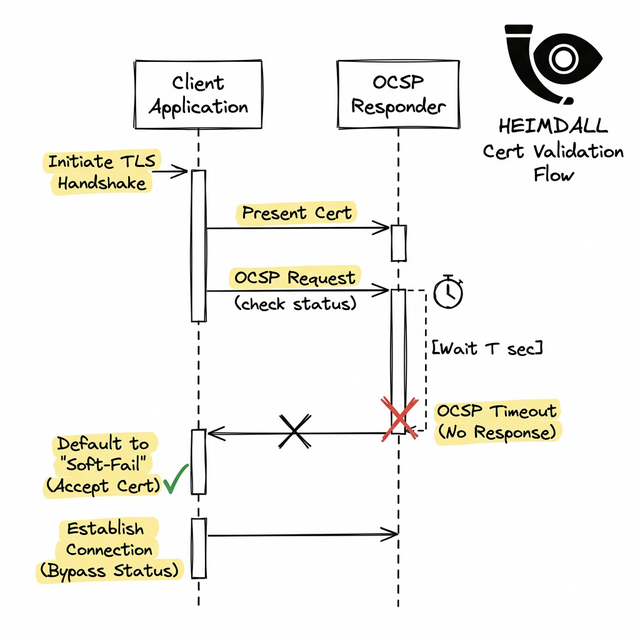
The fatal flaw of OCSP is latency and reliability. If a browser requires an OCSP check before loading a page, and the CA's responder is down or blocked by a firewall, what happens?
If the browser hard-fails, the website goes offline because of a third-party outage. To prevent taking down the internet during CA outages, browsers implemented 'soft-fail'. If the OCSP responder times out, the browser simply assumes the certificate is valid.
This means a network attacker who has a revoked, compromised certificate can simply block the client's OCSP requests, forcing a soft-fail and successfully impersonating the server.
Verifying OCSP Stapling
The solution to this is OCSP Stapling. Instead of the client asking the CA, your server asynchronously fetches a signed OCSP response from the CA and 'staples' it to the TLS handshake.
To debug and verify if your server is correctly stapling responses, use OpenSSL:
openssl s_client -connect yourdomain.com:443 -status < /dev/null | grep -A 17 'OCSP response:'
If it returns 'OCSP response: no response sent', your stapling is misconfigured, pushing the validation burden and latency back onto your users.
Ensuring Edge Validation
Managing stapling and assessing trust chains requires continuous external validation. Heimdall Observer systematically enforces deep TLS inspection from multiple vantage points. By using Heimdall to monitor your certificates, you gain definitive proof that your endpoints are serving valid, trustworthy cryptography that won't trigger hidden failures at the edge.
Ingeniero de infraestructura enfocado en DNS, redes y las capas invisibles que determinan si las aplicaciones son accesibles.
"Creamos Heimdall Observer para monitorizar los tipos de problemas que se tratan en este artículo."