How DNS Failures Cause Invisible Downtime
DNS failures are often invisible to internal monitoring systems. Learn how recursive resolution chains and latency can silently take down your infrastructure.
Observability platforms are designed to track what your systems are doing. But what happens when an outage occurs before a request even reaches your infrastructure edge? Your dashboards will confidently report 100% uptime, while your customers experience an unyielding blackout.
The Split-Horizon Dilemma
The reason your metrics lie is due to the split-horizon nature of cloud networking. Your internal Kubernetes pods or EC2 instances resolve internal service endpoints using a private VPC resolver (like AWS Route53 Resolver). Since the internal network is pristine, health checks between microservices succeed brilliantly.
But external customers rely on the public internet's recursive resolution chain to discover your public-facing Ingress.
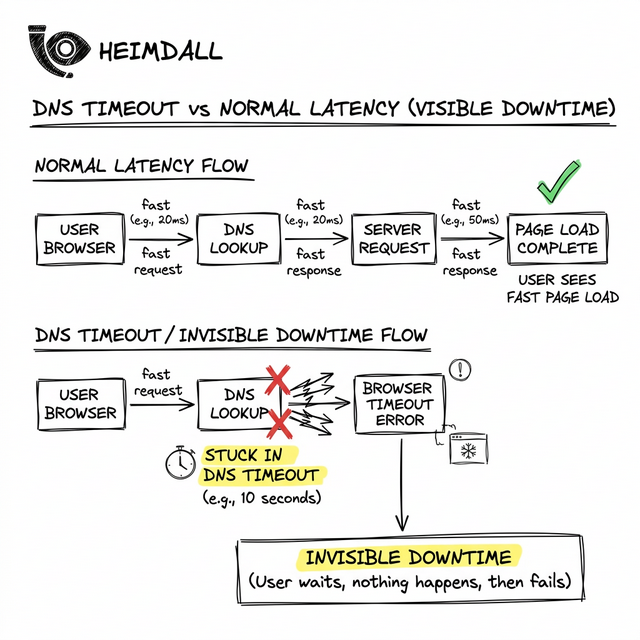
When the Front Door Disappears
An 'invisible' outage happens when the public authoritative records are disrupted. A classic example occurred during the 2021 Slack outage: an engineering team pushed a configuration that inadvertently stripped all A records for their main API domains.
Internally at Slack, the servers were humming, processing background jobs and maintaining open websocket connections. But no new clients could resolve the domain 'slack.com' to establish a handshake. The public internet simply forgot where Slack was hosted.
Isolating the Gap: Internal vs External Validation
To prove this discrepancy, you can write a simple test script. Instead of relying on a ping tool that uses your OS default config, you explicitly force a DNS lookup against your domain's public authoritative server:
nslookup -debug yourdomain.com ns1.your-dns-provider.com
If this command times out or returns NOERROR with 0 answers, your authoritative record layer has failed, irrespective of what Datadog is telling you.
Creating High-Fidelity External Context
Defeating inside-out blindness requires deploying probes outside of your cloud provider. Synthetic monitoring nodes must run from standalone ISP networks, repeatedly resolving your domain and asserting that the returned IPs actually belong to your Load Balancer's ASN.
Conclusion
When designing your reliability posture, never trust an internal health check to validate external reachability. The internet is a complex web of handoffs, and DNS is the very first one.
To automate this perspective, Heimdall Observer continuously audits your domains from global viewpoints, mapping your true public resolution health.
Ingénieur d'infrastructure axé sur le DNS, les réseaux et les couches invisibles qui déterminent si les applications sont accessibles.
"Nous avons conçu Heimdall Observer pour surveiller les types de problèmes abordés dans cet article."