What Causes SERVFAIL Errors in DNS
SERVFAIL is the most dreaded DNS error. Learn what causes it, how DNSSEC and lame delegations trigger it, and how to debug it.

If an NXDOMAIN response is the equivalent of an HTTP 404 (Not Found), then SERVFAIL is the HTTP 500 (Internal Server Error) of the DNS world. It is the most frustrating response an engineer can see because it is entirely opaque: it simply tells you that the recursive server gave up trying to find an answer.
Why Revolvers Give Up
A SERVFAIL is almost never generated by your authoritative nameserver directly. It is a surrender flag raised by a recursive resolver (like an ISP or Google DNS). When the resolver tries to follow the delegation chain from the Root down to your nameservers, it expects a clean handoff.
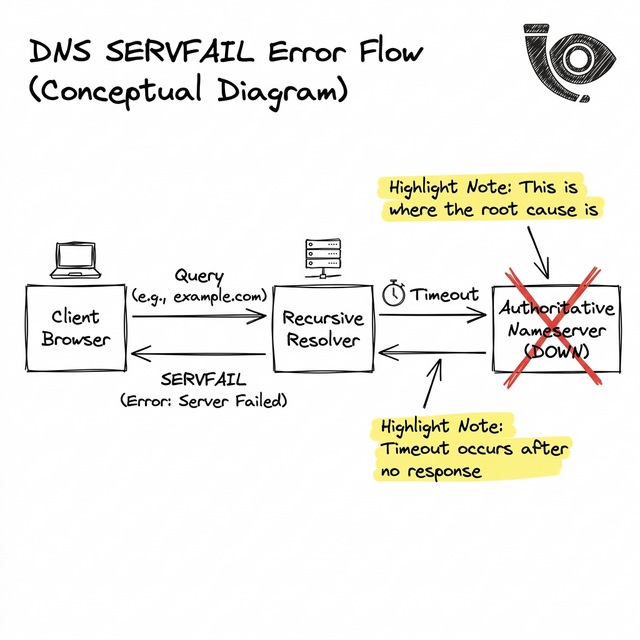
If the handoff involves a timeout, a connection reset, or cryptographic validation failure, the recursive resolver terminates the process and returns a SERVFAIL to the end user's browser, instantly breaking the connection.
The Two Primary Culprits
While network partitions and massive DDoS attacks on your DNS provider can trigger SERVFAILs due to timeouts, the vast majority of these errors in modern infrastructure are self-inflicted wounds:
1. The DNSSEC Footgun
DNSSEC adds cryptographic signatures to DNS records to prevent spoofing. However, if your engineering team rotates your authoritative signing keys without updating the DS (Delegation Signer) record at your domain registrar, the entire internet will assume your domain has been hijacked.
Recursive resolvers will intentionally return a SERVFAIL to block users from what it believes is a compromised zone.
2. Lame Delegations
If your registrar points to four nameservers (e.g., ns1 through ns4 at Route53), but you accidentally deleted the hosted zone in your AWS account, those nameservers will refuse to answer for your domain. The resolver detects this discrepancy and returns a SERVFAIL.
Surgical Debugging
To determine if a SERVFAIL is caused by DNSSEC, you should use the validation tracing tools built into `dig`:
dig +cd +short yourdomain.com
The `+cd` (Checking Disabled) flag tells the recursive resolver to skip DNSSEC validation. If the query succeeds with this flag, but fails without it, you have definitively proven that your cryptography is broken, and you must immediately pause DNSSEC at your registrar to restore traffic.
Conclusion
SERVFAIL represents a hard breakage in the trust chain of the internet.
With Heimdall Observer, you don't have to wait for users to report connection drops. By synthetically asserting the validity of your DNSSEC signatures and delegation chains globally, Heimdall alerts you to cryptographic misconfigurations long before a resolver resorts to throwing a SERVFAIL.
Ingénieur d'infrastructure axé sur le DNS, les réseaux et les couches invisibles qui déterminent si les applications sont accessibles.
"Nous avons conçu Heimdall Observer pour surveiller les types de problèmes abordés dans cet article."