How to Monitor Automated Let's Encrypt Renewals
Automated renewals fail silently. Learn the common failure modes of ACME challenges and why you must monitor the endpoint, not the cronjob.

The introduction of Let's Encrypt and the ACME protocol drastically changed how we handle TLS. By dropping validity periods to 90 days and providing tooling like Certbot, the industry shifted from manual calendar reminders to automated cronjobs.
However, automation introduces a new category of failure: silent failures. If an automated script breaks, it doesn't complain; it just stops working. And 30 days later, your website goes offline.
How ACME Automations Fail
The ACME protocol requires your server to prove control over a domain. It does this via challenges, typically HTTP-01 or DNS-01. These mechanisms are highly sensitive to infrastructure changes.
| Failure Type | Symptom | Detection Method |
|---|---|---|
| WAF Blocking | HTTP-01 challenge fails | Let's Encrypt returns 403 Forbidden |
| DNS Propagation | DNS-01 TXT record too slow | Challenge completes before record is visible |
| Rate Limiting | Hits max failed attempts | ACME API returns 429 Too Many Requests |
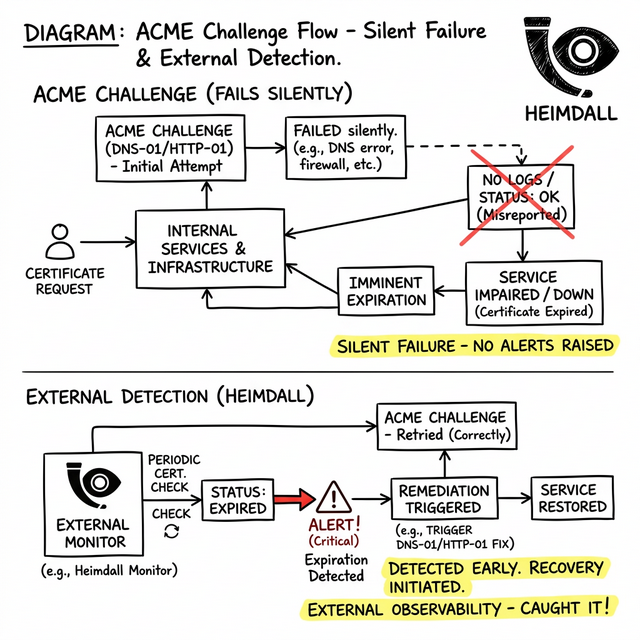
The Fallacy of Log Monitoring
Engineers often try to solve this by installing agents that grep cron logs for the word 'success'. This is a dangerous anti-pattern. Even if Certbot successfully negotiates a new certificate and saves the .pem files to disk, your application might fail to reload.
If an NGINX process refuses to gracefully reload due to a syntax error elsewhere in its config, the new certificate will sit on the hard drive while the active process continues serving the expiring, old certificate from memory. Your logs say success, but your users will still see an outage.
Debugging the Endpoint
You must audit the actual network output. You can use curl to extract the exact expiration date directly from the active socket:
curl -vI https://yourdomain.com 2>&1 | grep 'expire date'
If this date is within 20 days and you use Let's Encrypt, your automation is broken.
The Proper Monitoring Strategy
The only reliable way to monitor automated certificates is from the outside. By integrating Heimdall Observer into your reliability stack, you shift from hoping your cronjobs work, to cryptographically verifying the endpoint. Heimdall continuously interrogates your public-facing TLS layer, instantly catching failed renewals well before the expiration date breaches the critical threshold.
Ingénieur d'infrastructure axé sur le DNS, les réseaux et les couches invisibles qui déterminent si les applications sont accessibles.
"Nous avons conçu Heimdall Observer pour surveiller les types de problèmes abordés dans cet article."